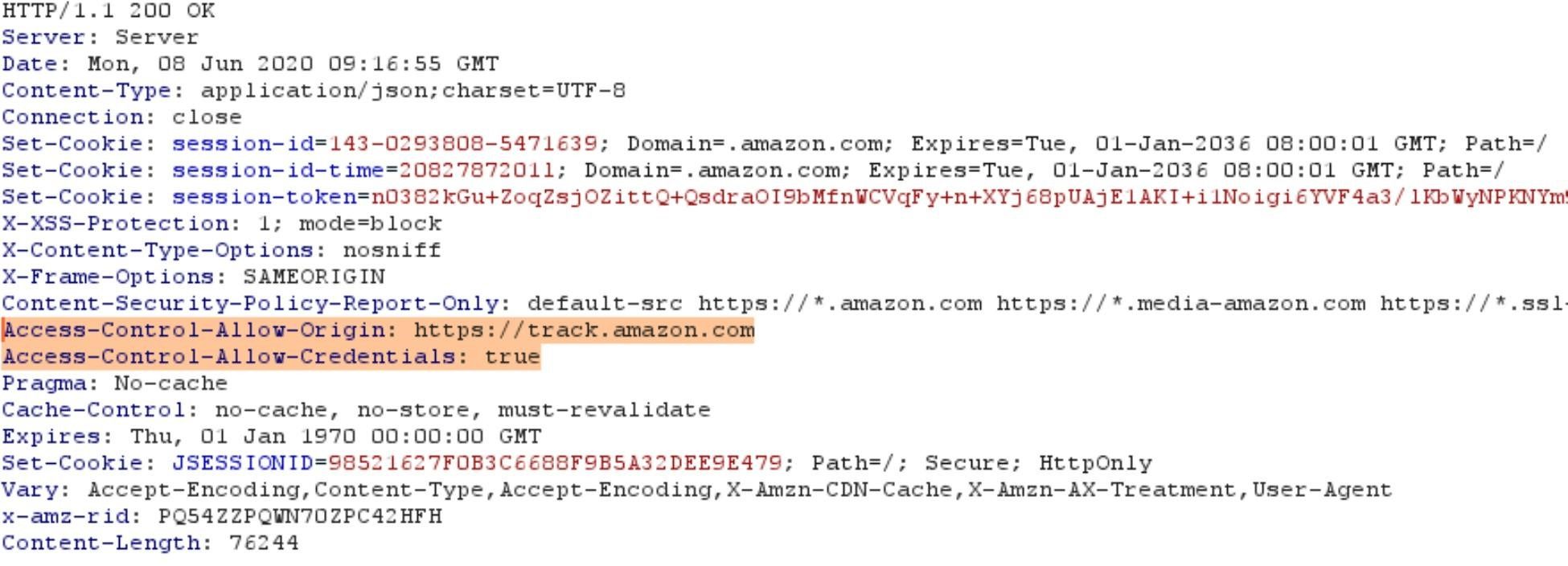
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
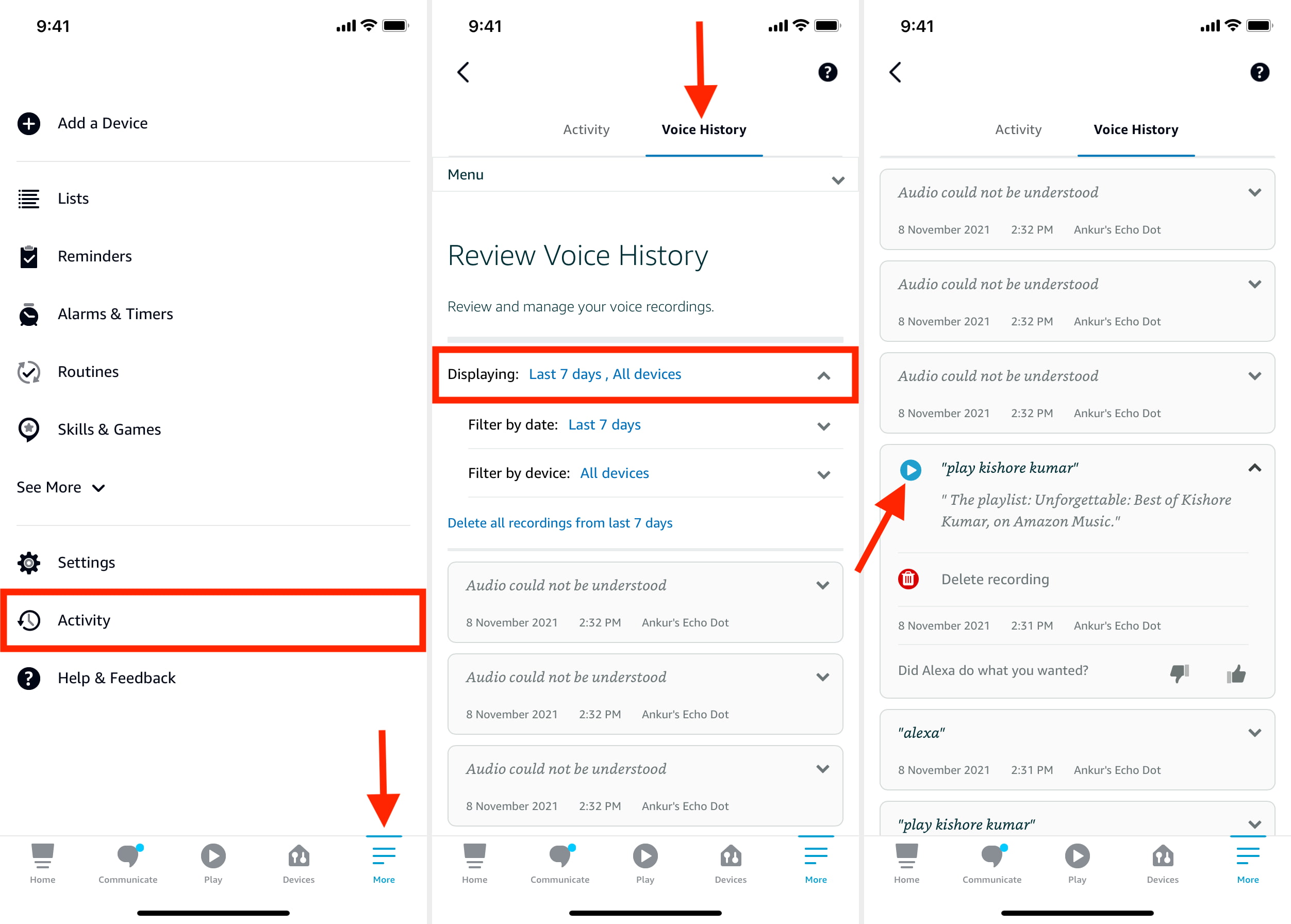
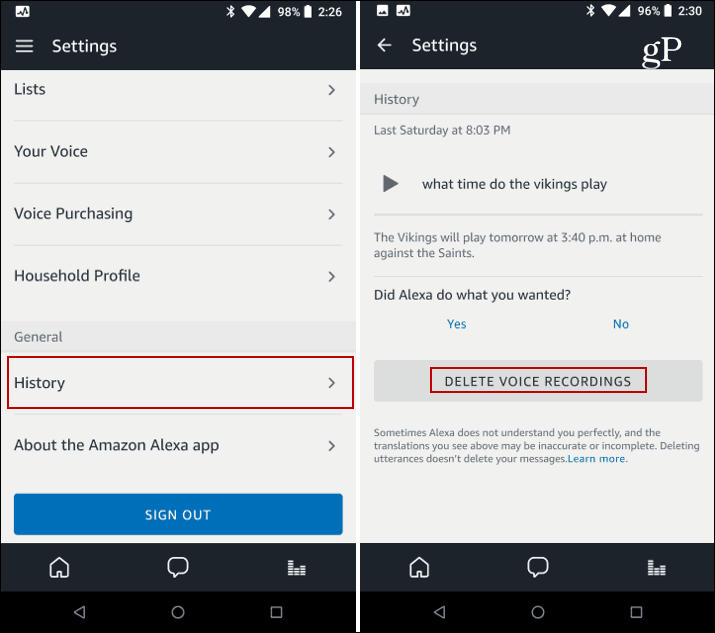
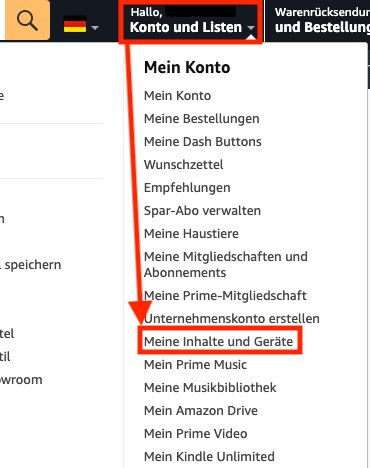
So hören, löschen und bitten Sie Amazon, Ihre Alexa-Sprachaufzeichnungen nicht zu speichern - DE Atsit